Under a CYBER ATTACK? call (877) 248-4991
CISS Professional Services
CISS is a leading provider of security solutions, offering comprehensive architectural and engineering support. With a dedicated focus on cybersecurity for the past two decades, we have developed expertise across various industry verticals, including Finance, Legal, Manufacturing, Public Sector, and Retail.
Whether you require contract services or convenient monthly billable solutions, our certified experts are here to assist you. We can effectively tackle projects of any size, helping you stay on target with both budgets and deadlines. Partner with CISS for the expertise you desire.
CISS a MSP for the future
Managed Service Providers (MSPs) offer a range of benefits to businesses looking to outsource their IT needs. MSPs provide a team of experts who can manage and maintain your IT infrastructure, freeing up your internal IT staff to focus on more strategic initiatives. MSPs also provide 24/7 support, which ensures that your IT systems are always up and running.
MSPs like CISS provide a range of cybersecurity services, including endpoint protection, network security, email security, and more. By partnering with an MSP like CISS, you can benefit from their expertise and experience in the field of cybersecurity, which helps to reduce the risk of cyberattacks and data breaches.
Monthly billing is a convenient option offered by CISS. Monthly billing allows businesses to pay for the services they need on a monthly basis, which helps to reduce upfront costs and improve cash flow. Monthly billing also provides greater flexibility, as businesses can adjust their services as needed to meet changing business requirements.
In summary, partnering with CISS provides a range of benefits, including access to a team of experts, 24/7 support, and a range of cybersecurity services. Monthly billing is a convenient option that helps to reduce upfront costs and improve cash flow, while providing greater flexibility
Support Services
CISS offers a full selection of support services, from simple health checks to emergency response, to ensure that your IT infrastructure is always up and running. Our team of experts has the expertise to reduce your response times and avert larger potential issues, providing you with peace of mind. CISS has extensive experience in network and security matters, including how they tie into your overall risk management strategy and compliance models.
If you are an existing client seeking support just use this link or click support in the menu at the top of the page.
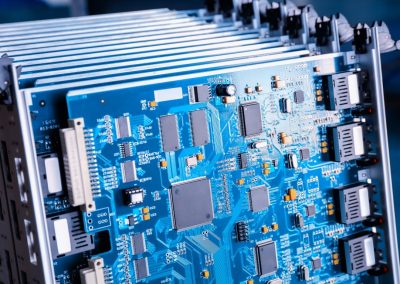
Hardware when you need it
Computer network hardware devices can be difficult to obtain at times, and it can be frustrating when you are unable to get what you need in a timely manner. CISS can help you procure any network hardware, server equipment, desktops, and laptops that you may need. Simply let us know what you are looking for, and we will provide you with a timely quote for your needs.
All Your Trusted Vendors Under One Umbrella
Sophos
CISS is a Platinum Partner with Sophos with certified Sophos Engineers and Architects on staff.
Cybernetics logo no bg
CISS has been partnered with Cybernetics with dozens of successful deployments.
Juniper
CISS is proud to welcome Juniper into our partner space. We look forward to many years of success with these quality units.